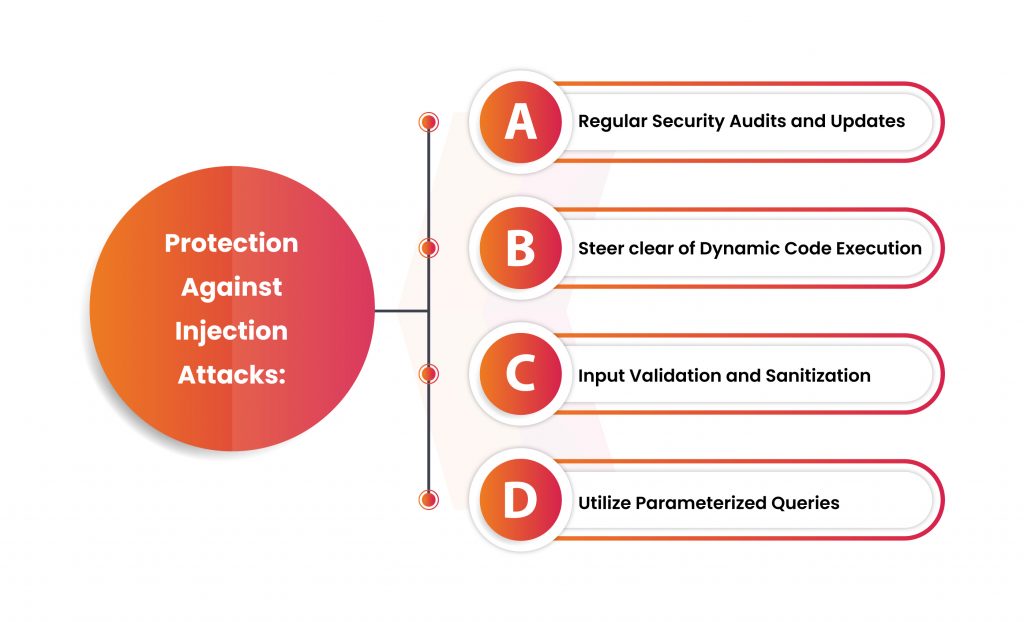
How Can Injection Attacks Be Prevented - This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. Developers can prevent sql injection vulnerabilities in web applications by utilizing. Once exploited, sql injection attacks can lead to: Prevent malicious sql input from being included in executed queries. Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. To avoid sql injection flaws, developers need to:
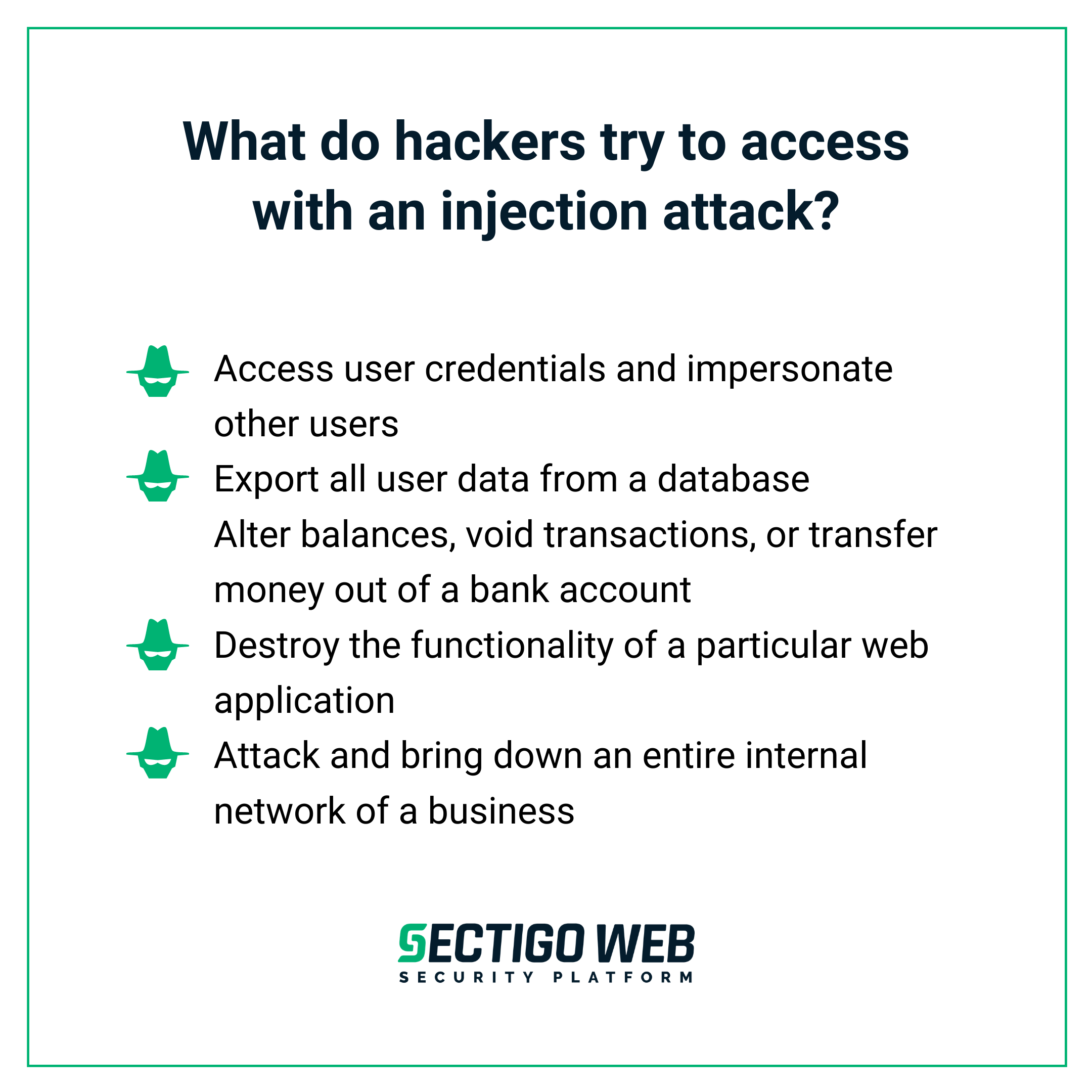
Once exploited, sql injection attacks can lead to: This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. To avoid sql injection flaws, developers need to: Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. Prevent malicious sql input from being included in executed queries. Developers can prevent sql injection vulnerabilities in web applications by utilizing.
In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. Once exploited, sql injection attacks can lead to: Prevent malicious sql input from being included in executed queries. This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. Developers can prevent sql injection vulnerabilities in web applications by utilizing. To avoid sql injection flaws, developers need to: Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity.
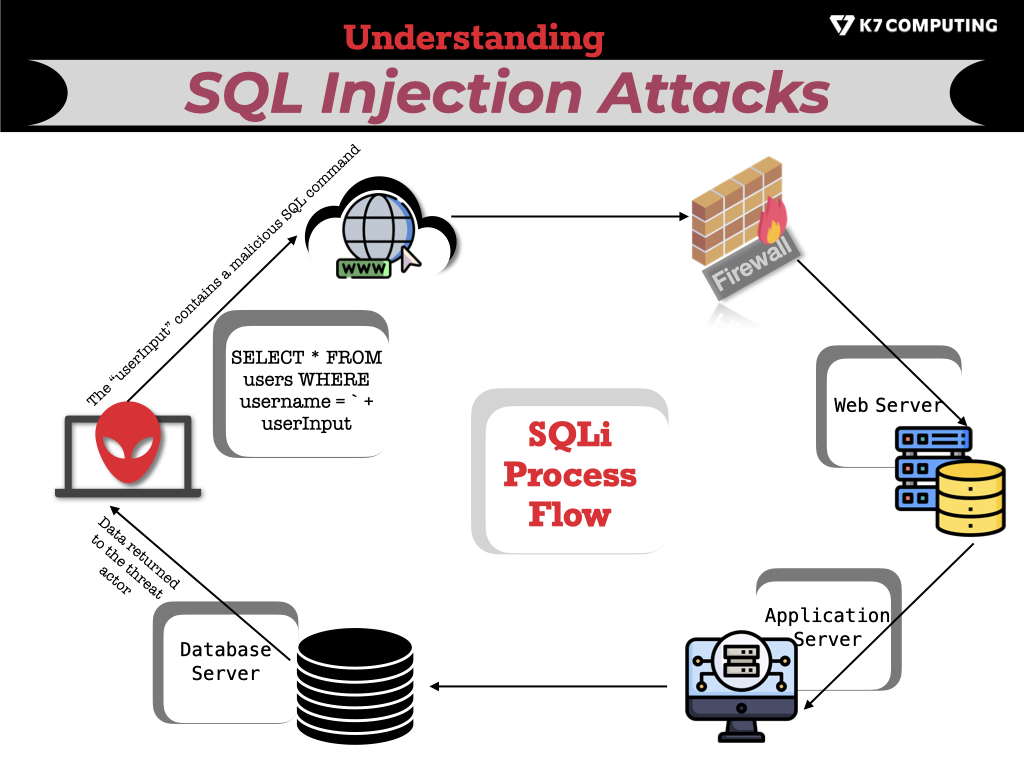
Understanding SQL Injection Attacks Sectigo® Official
While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. Developers can prevent sql injection vulnerabilities in web applications by utilizing. In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. To avoid sql injection flaws, developers need.
How can SQL injection be prevented?
In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. Developers can prevent sql injection vulnerabilities in web applications by utilizing. Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. Prevent malicious sql input from being included in executed queries. To avoid.
Understanding Sql Injection Attacks NBKomputer
To avoid sql injection flaws, developers need to: Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. Prevent malicious sql input from being included in executed queries. Developers can prevent sql injection.
Injection attacks FineProxy Glossary
While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. To avoid sql injection flaws, developers need to: Once exploited, sql injection attacks can lead to: Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. Prevent malicious sql input from being included.
How Injection Attacks Can Cripple Your Business? Kratikal Blogs
This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies. Prevent malicious.
TryHackMe Injection Attacks
Once exploited, sql injection attacks can lead to: Prevent malicious sql input from being included in executed queries. Developers can prevent sql injection vulnerabilities in web applications by utilizing. To avoid sql injection flaws, developers need to: This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications.
How Injection Attacks Can Cripple Your Business? Kratikal Blogs
Prevent malicious sql input from being included in executed queries. This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. To avoid sql injection flaws, developers need to: While sql injection is one of the most prevalent api threats, it can be effectively avoided with the right prevention strategies..
Sql injection attacks PPT
Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. Developers can prevent sql injection vulnerabilities in web applications by utilizing. To avoid sql injection flaws, developers need to: Prevent malicious sql input from being included in executed queries. This article is focused on providing clear, simple, actionable guidance for preventing the entire category.
Injection Attacks The Free Guide Cybr
In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications. Once exploited, sql injection attacks can lead to: While sql injection is one of the most prevalent api.
How can SQL injection be prevented?
Developers can prevent sql injection vulnerabilities in web applications by utilizing. In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. Prevent malicious sql input from being included in executed queries. While sql injection is one of the most prevalent api threats, it can be effectively avoided with the.
Prevent Malicious Sql Input From Being Included In Executed Queries.
Ensuring robust protection against sql injection means assurance of continuity in operational security and business integrity. To avoid sql injection flaws, developers need to: Once exploited, sql injection attacks can lead to: This article is focused on providing clear, simple, actionable guidance for preventing the entire category of injection flaws in your applications.
While Sql Injection Is One Of The Most Prevalent Api Threats, It Can Be Effectively Avoided With The Right Prevention Strategies.
In this article, we look at different types of injection attacks, including the infamous sql injection attacks, show how attackers take. Developers can prevent sql injection vulnerabilities in web applications by utilizing.