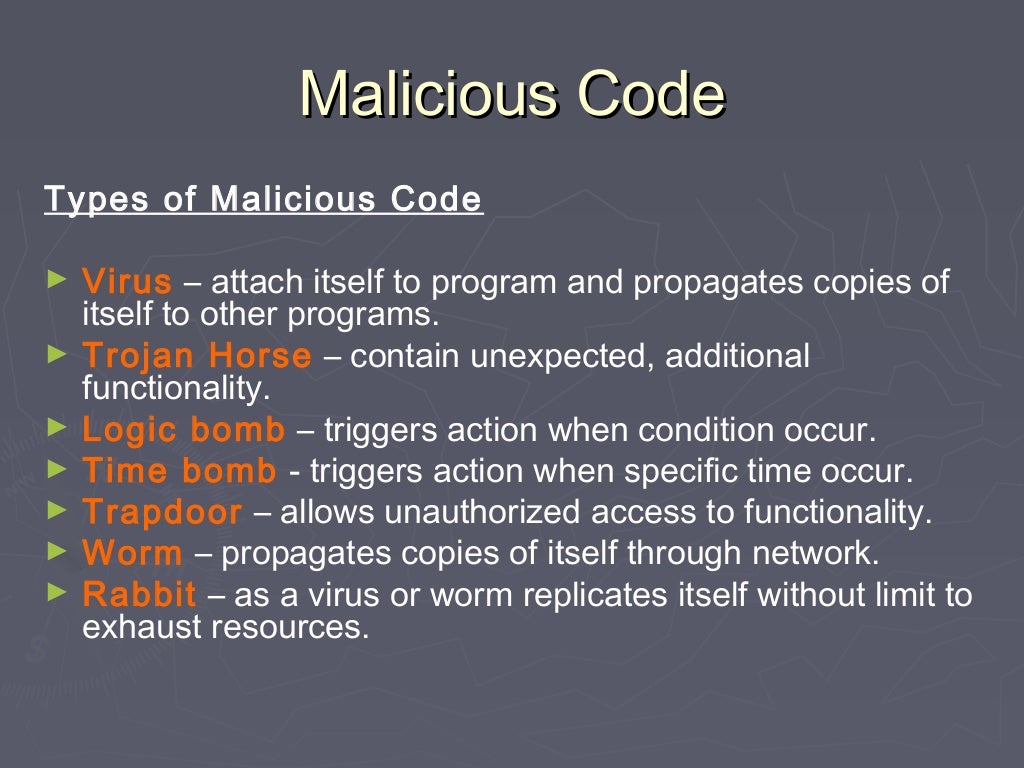
How Can You Prevent Viruses In Malicious Code - Do not have the potential to damage. At the center of most cyber attacks and security breaches are a sinister application called malicious code. Matt is a government employee who needs to share a document containing source selection. Your meeting notes are unclassified. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. How can you prevent viruses and malicious code? Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. This means that your notes.
At the center of most cyber attacks and security breaches are a sinister application called malicious code. Matt is a government employee who needs to share a document containing source selection. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. Do not have the potential to damage. How can you prevent viruses and malicious code? This means that your notes. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. Your meeting notes are unclassified.
Your meeting notes are unclassified. This means that your notes. Matt is a government employee who needs to share a document containing source selection. How can you prevent viruses and malicious code? At the center of most cyber attacks and security breaches are a sinister application called malicious code. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. Do not have the potential to damage. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,.
Malicious Code Project by 21BPerry0116
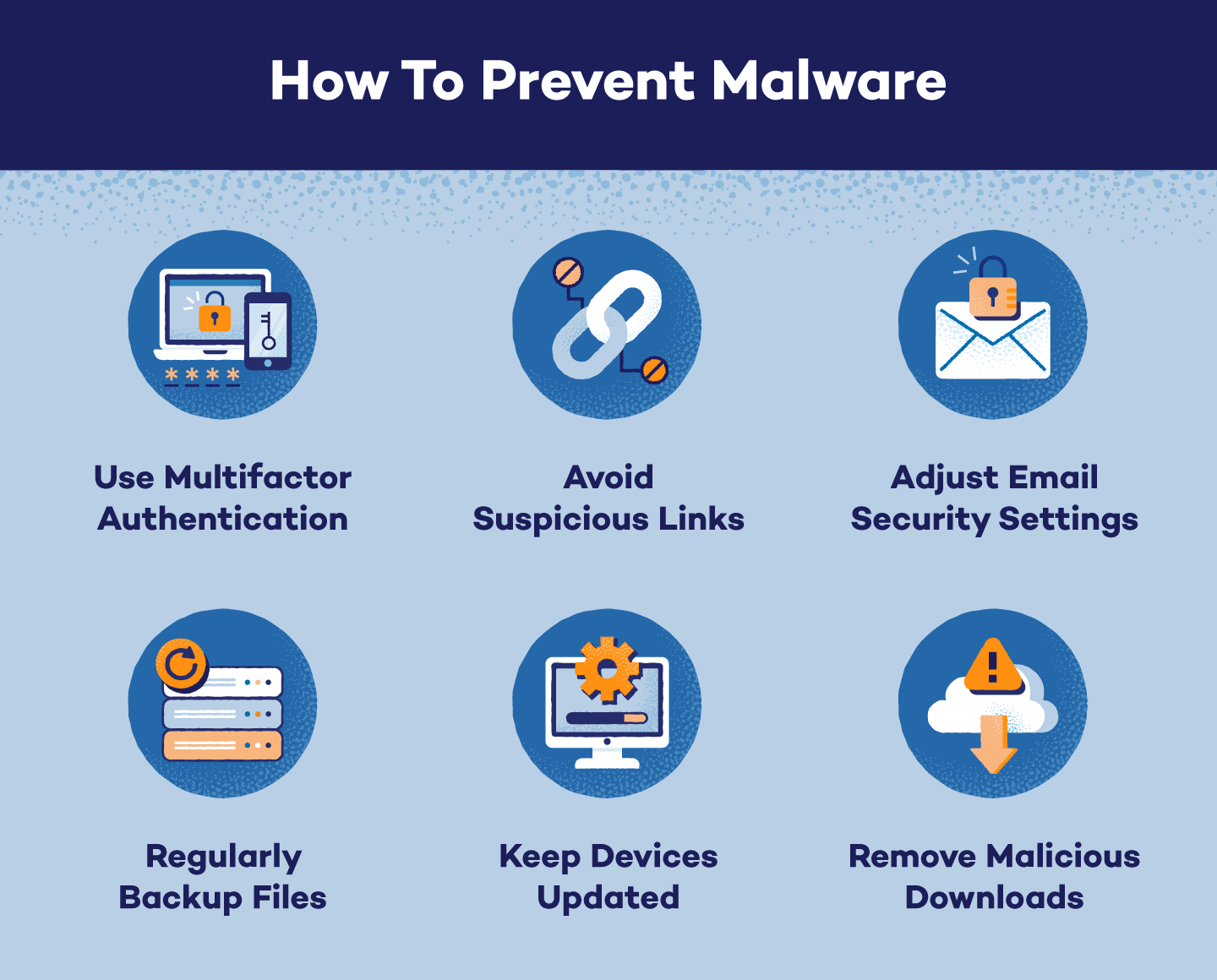
How can you prevent viruses and malicious code? Matt is a government employee who needs to share a document containing source selection. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. This means that your notes. Do not have the potential to damage.
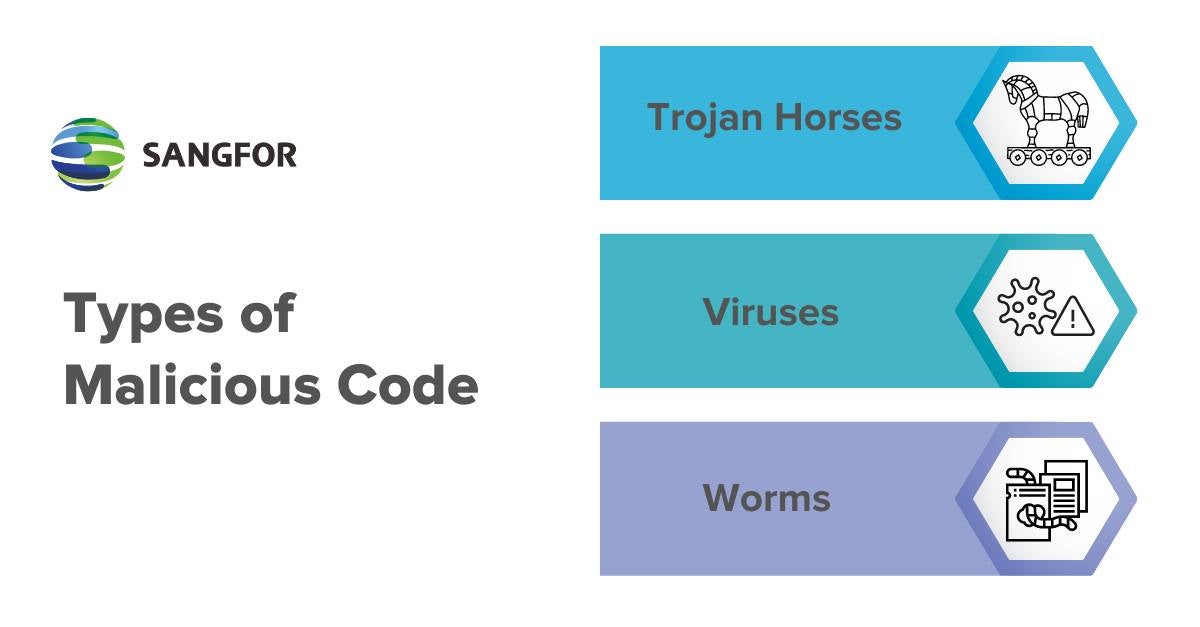
What is Malicious Code and How to Avoid It Sangfor
This means that your notes. At the center of most cyber attacks and security breaches are a sinister application called malicious code. Do not have the potential to damage. Your meeting notes are unclassified. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files.
Want to Prevent Computer Viruses? (7 Stealthy Tips) Shred Cube
How can you prevent viruses and malicious code? Matt is a government employee who needs to share a document containing source selection. At the center of most cyber attacks and security breaches are a sinister application called malicious code. Do not have the potential to damage. This means that your notes.
Copy of Malicious code by janevitullo
Your meeting notes are unclassified. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. This means that your notes. Matt is a government employee who needs to share a document containing source selection.
Prevent Malware Infections With Windows Malicious Software
How can you prevent viruses and malicious code? Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. At the center of most cyber attacks and security breaches are a sinister application called malicious code. Your meeting notes are unclassified. Some common examples include viruses that attach to files and spread, worms that reproduce themselves.
Virus and Malicious Code Chapter 5
Matt is a government employee who needs to share a document containing source selection. How can you prevent viruses and malicious code? This means that your notes. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. Do not have the potential to damage.
What Everybody Ought To Know About How To Prevent Getting Computer
Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. At the center of most cyber attacks and security breaches are a sinister application called malicious code. This means that your notes. How can you prevent viruses and malicious code? Matt is a government employee who needs to share a document containing.
Avoid Malicious Code Secure Your Systems!
Do not have the potential to damage. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. How can you prevent viruses and malicious code? Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. At the center of most cyber attacks and security.
Beware of hidden malicious code inside your templates ChuchoWebmaster
Matt is a government employee who needs to share a document containing source selection. This means that your notes. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. Do not have the potential to damage.
Malicious Code What is it and How to Prevent it 2025 Guide
How can you prevent viruses and malicious code? This means that your notes. Your meeting notes are unclassified. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan. Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files.
Matt Is A Government Employee Who Needs To Share A Document Containing Source Selection.
Do not have the potential to damage. At the center of most cyber attacks and security breaches are a sinister application called malicious code. How can you prevent viruses and malicious code? Both viruses and malicious code can infiltrate your systems through vulnerabilities, phishing, or infected files.
Your Meeting Notes Are Unclassified.
This means that your notes. Viruses, trojan horses, spyware, and other types of malicious code can cause devastating damage to your computer, network,. Some common examples include viruses that attach to files and spread, worms that reproduce themselves across networks, trojan.