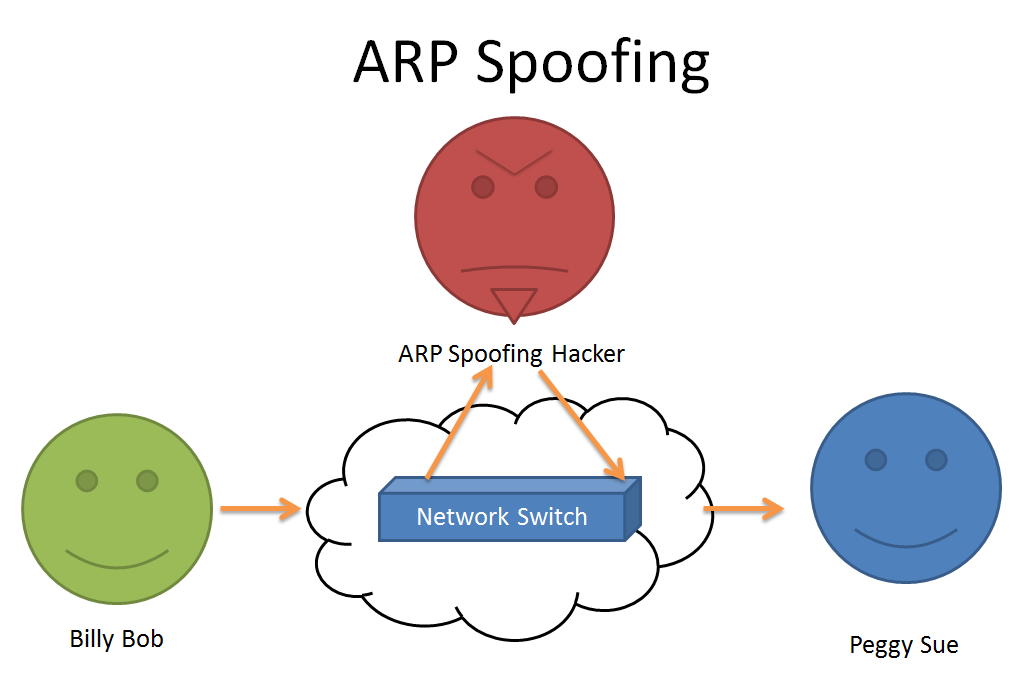
How To Prevent Arp Spoofing - Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental.
Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and.
Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing.
Demystifying ARP Spoofing Blog
Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental.
ARP Spoofing What is it and how can I protect myself?
Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and.
How to Prevent ARP Spoofing? Cybers Guards
Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing.
ARP Spoofing Attack PDF
Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental.
GitHub hayeong0/ARP_spoofing ARP_spoofing tool
Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and.
How To Prevent ARP Spoofing Database Doctor
Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and.
ARP SPOOFING Octa Networks
Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and.
Preventing & Identifying ARP Poisoning or Spoofing Attacks
Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing.
GitHub hayeong0/ARP_spoofing ARP_spoofing tool
Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental.
GitHub hayeong0/ARP_spoofing ARP_spoofing tool
Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental. Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Fortunately, you can implement a number of procedures and tools as part of your incident response plan to prevent arp spoofing.
Fortunately, You Can Implement A Number Of Procedures And Tools As Part Of Your Incident Response Plan To Prevent Arp Spoofing.
Learn how arp spoofing, also known as arp poisoning, poses significant security risks by allowing attackers to intercept and. Arp spoofing is a malicious attack that exploits vulnerabilities in the address resolution protocol (arp), a fundamental.