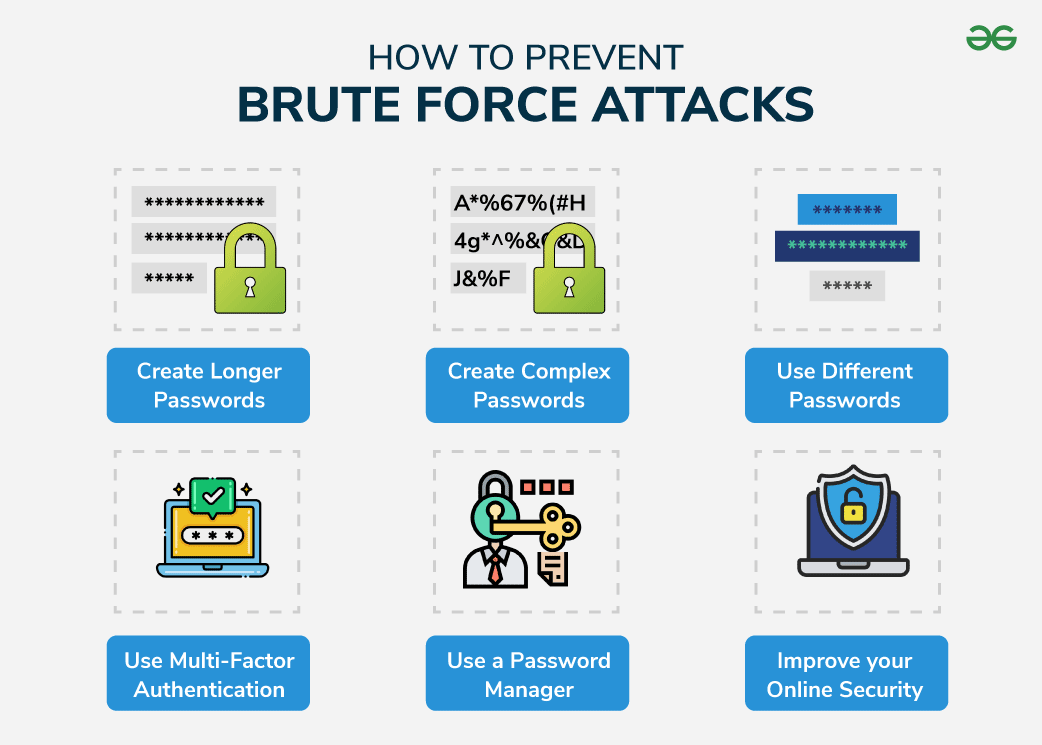
How To Prevent Brute Force Attacks - Brute force attacks leave obvious clues for server operators. Hackers use trial and error methods to get the user account credentials and steal the information on the. This guide explains 8 methods. Read this article to learn more about how to prevent brute force attacks from taking. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. How to identify brute force attacks. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. If system administrators notice a sudden increase in. Most server software automatically logs failed login attempts. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords.
Most server software automatically logs failed login attempts. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. Hackers use trial and error methods to get the user account credentials and steal the information on the. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. How to identify brute force attacks. This guide explains 8 methods. Brute force attacks leave obvious clues for server operators. Read this article to learn more about how to prevent brute force attacks from taking. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. If system administrators notice a sudden increase in.
This guide explains 8 methods. Hackers use trial and error methods to get the user account credentials and steal the information on the. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. Brute force attacks leave obvious clues for server operators. Most server software automatically logs failed login attempts. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. If system administrators notice a sudden increase in. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. How to identify brute force attacks. Read this article to learn more about how to prevent brute force attacks from taking.
How To Prevent Brute Force Attacks With 8 Easy Tactics PhoenixNAP KB
Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. Most server software automatically logs failed login attempts. This guide explains 8 methods. Read this article to learn more about how to prevent brute force attacks from taking. Brute force attacks leave obvious clues for server operators.
How to Prevent Brute Force Attacks?
Hackers use trial and error methods to get the user account credentials and steal the information on the. Read this article to learn more about how to prevent brute force attacks from taking. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. If system administrators notice a sudden increase in..
How To Prevent Brute Force Attacks? Wp Safe Zone
A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. How to identify brute force attacks. Brute force attacks leave obvious clues for server operators. If system administrators notice a sudden increase in.
SSH Hardening to Prevent BruteForce Attacks
Read this article to learn more about how to prevent brute force attacks from taking. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. How to identify brute force attacks. This guide explains 8 methods. Hackers use trial and error methods to get the user account credentials and steal the.
How To Prevent Brute Force Attacks With 8 Easy Tactics PhoenixNAP KB
A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. If system administrators notice a sudden increase in. Read this article to learn more about how to prevent brute force attacks.
How to Prevent Brute Force Attacks Programming Cube
If system administrators notice a sudden increase in. Most server software automatically logs failed login attempts. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent. Read this article to learn more about how to prevent brute force attacks from taking. How to identify brute force attacks.
How to prevent brute force attacks
This guide explains 8 methods. Most server software automatically logs failed login attempts. How to identify brute force attacks. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. Brute force attacks leave obvious clues for server operators.
How to Prevent Brute Force Attacks Top Strategies SSL Dragon
This guide explains 8 methods. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. If system administrators notice a sudden increase in. Most server software automatically logs failed login attempts. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures.
How to Prevent Brute Force Attacks Top Strategies SSL Dragon
Hackers use trial and error methods to get the user account credentials and steal the information on the. How to identify brute force attacks. A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. If system administrators notice a sudden increase in. Brute force attacks are increasingly accounting for the majority.
How To Prevent Brute Force Attacks?
A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures. How to identify brute force attacks. Brute force attacks leave obvious clues for server operators. Read this article to learn more about how to prevent.
How To Identify Brute Force Attacks.
Most server software automatically logs failed login attempts. Read this article to learn more about how to prevent brute force attacks from taking. Hackers use trial and error methods to get the user account credentials and steal the information on the. Prevent brute force attacks by learning how to identify them and implementing the right cybersecurity measures.
This Guide Explains 8 Methods.
A brute force attack is an attack where attackers follow a brute force approach to hack usernames and passwords. If system administrators notice a sudden increase in. Brute force attacks leave obvious clues for server operators. Brute force attacks are increasingly accounting for the majority of cyberattacks across the world as remote work becomes more prevalent.