Prevent Detect Respond - Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Develop and implement the appropriate. The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Ensure risk responses are identified and prioritized, executed, and results monitored. Together, these functions provide a. Detect and analyse cyber security events to identify cyber security incidents. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes.
The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Ensure risk responses are identified and prioritized, executed, and results monitored. Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Together, these functions provide a. Detect and analyse cyber security events to identify cyber security incidents. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes.
Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Together, these functions provide a. The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Detect and analyse cyber security events to identify cyber security incidents. Ensure risk responses are identified and prioritized, executed, and results monitored.
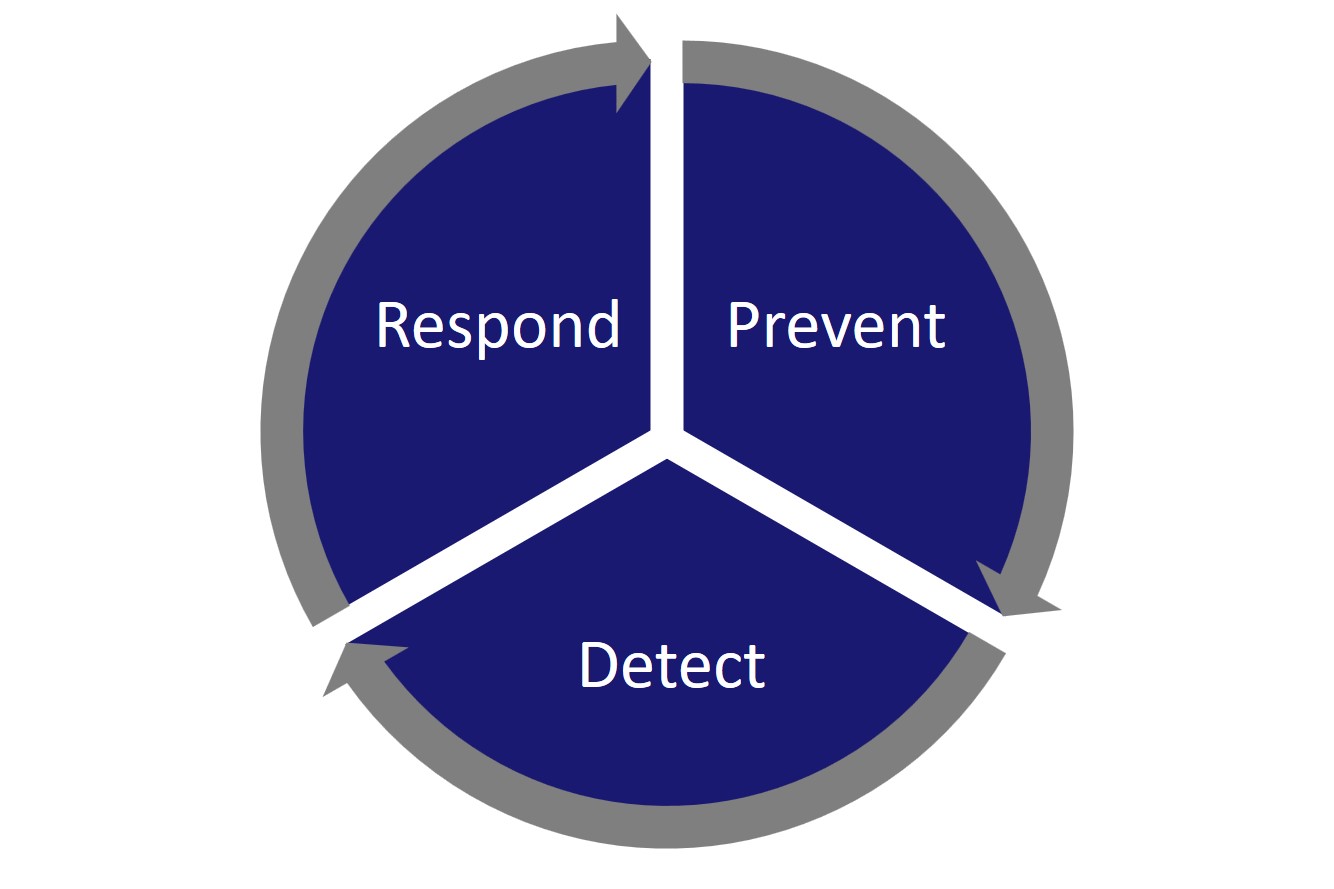
Prevent, Detect & Respond ICS
Ensure risk responses are identified and prioritized, executed, and results monitored. Detect and analyse cyber security events to identify cyber security incidents. The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Together, these functions provide a. Develop and implement the appropriate.
The PreventDetectRecover Cycle Cloud Gal 42
Ensure risk responses are identified and prioritized, executed, and results monitored. Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Together, these functions provide a. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes.
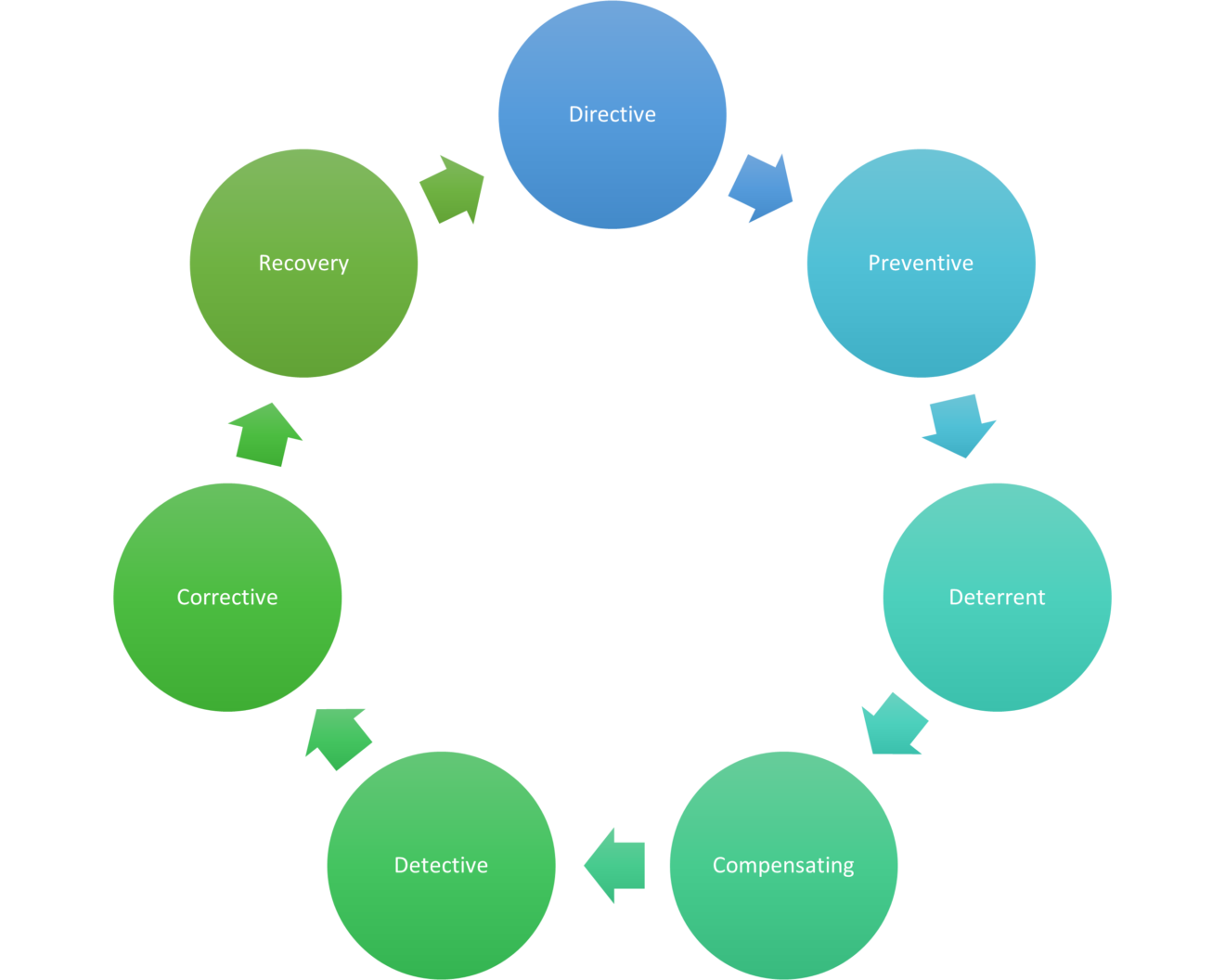
Identify, Prevent, Detect, Respond, and Recover BL King
Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Detect and analyse cyber security events to identify cyber security incidents. Develop and implement the appropriate. Ensure risk responses are identified and prioritized, executed, and results monitored. Learn how the detect function defines the appropriate activities to identify the occurrence of a.
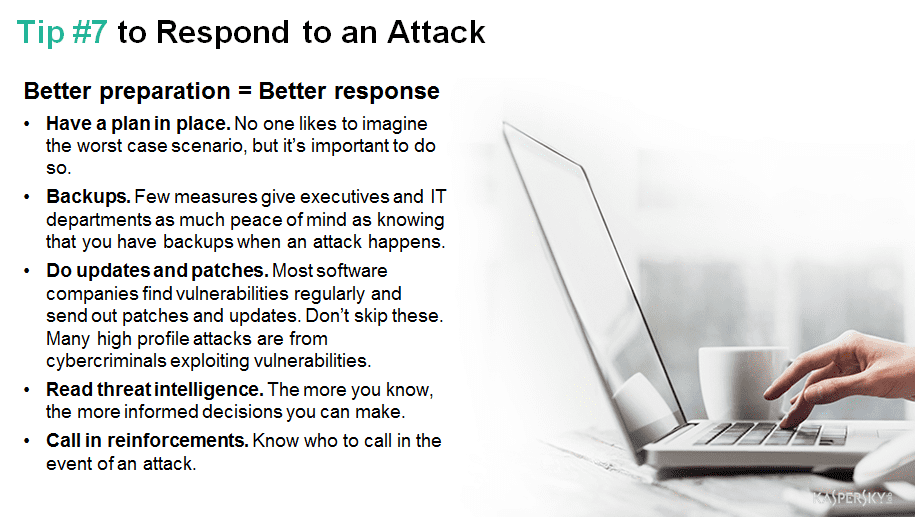
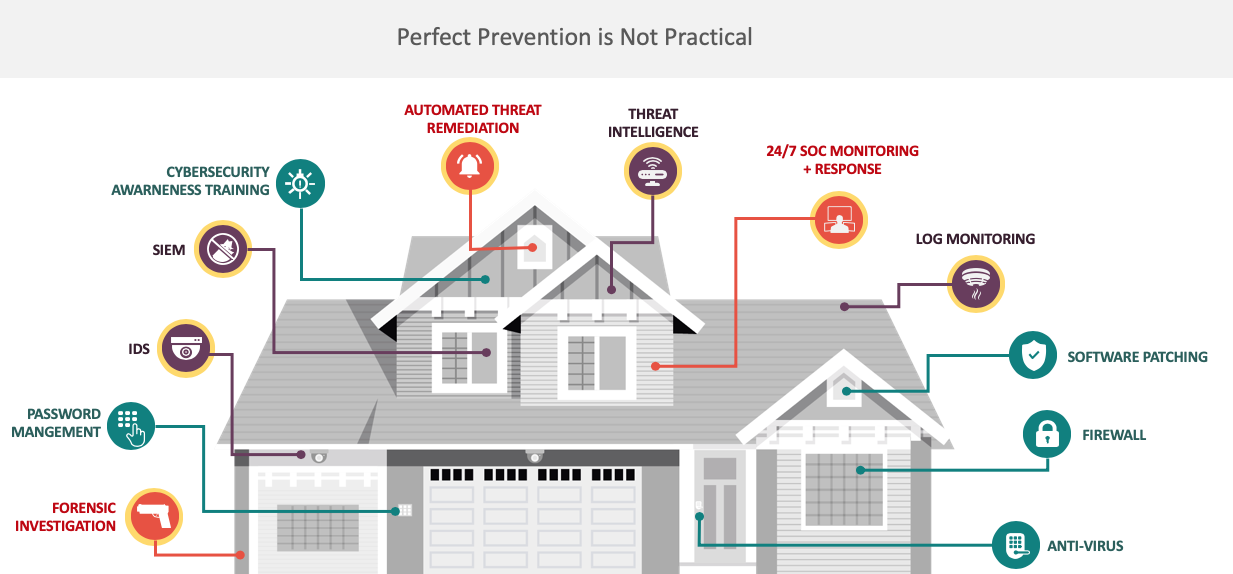
Predict, Prevent, Detect and Respond 8 Tips to Secure Your Business
Together, these functions provide a. Detect and analyse cyber security events to identify cyber security incidents. Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Ensure risk responses are identified and prioritized, executed, and results monitored.
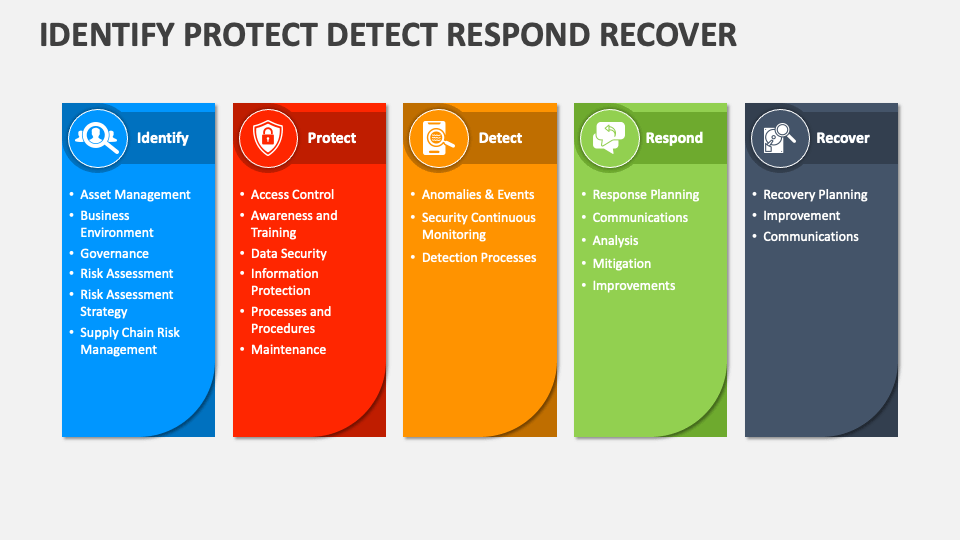
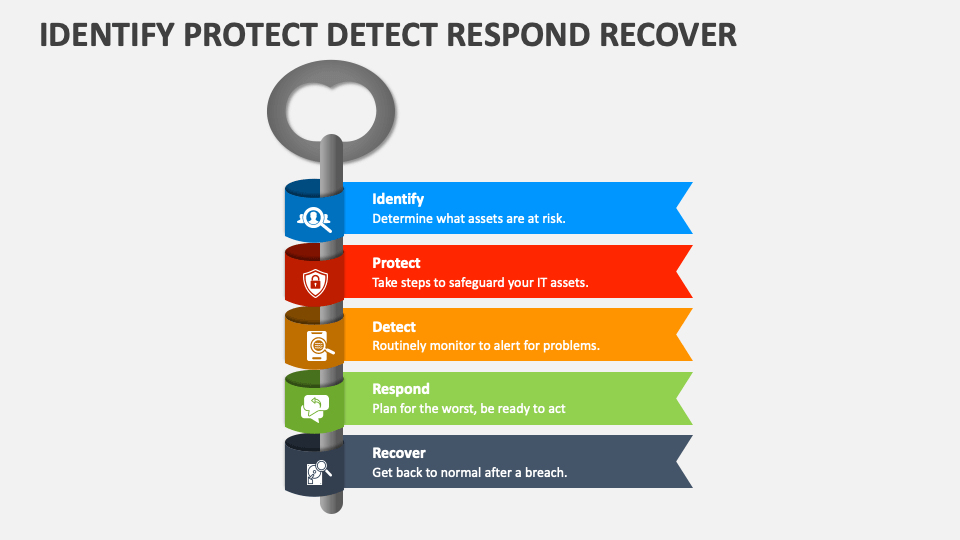
Identify Protect Detect Respond Recover PowerPoint Presentation Slides
The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Detect and analyse cyber security events to identify cyber security incidents. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Together, these functions provide a. Develop and implement the appropriate.
Identify Protect Detect Respond Recover PowerPoint Presentation Slides
Ensure risk responses are identified and prioritized, executed, and results monitored. The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Detect and analyse cyber security events to identify cyber security incidents.
Prevent, Detect, and Respond for True Security MSSP Alert
Develop and implement the appropriate. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. The csf 2.0 is organized by six functions — govern, identify, protect, detect, respond, and recover. Detect and analyse cyber security events to identify cyber security incidents. Together, these functions provide a.
Identify Protect Detect Respond Recover Business powerpoint templates
Ensure risk responses are identified and prioritized, executed, and results monitored. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Together, these functions provide a. Detect and analyse cyber security events to identify cyber.
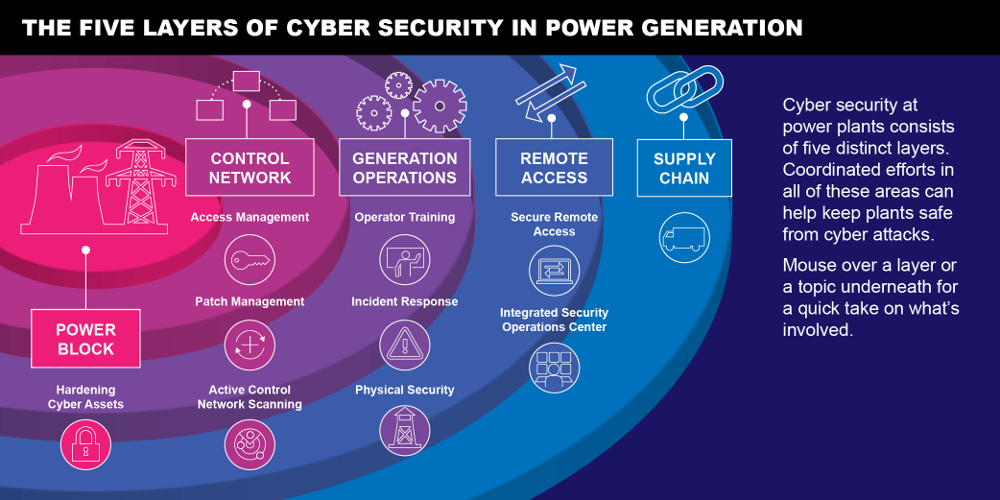
Protect, Detect, Respond, Recover EPRI Journal EPRI Journal
Ensure risk responses are identified and prioritized, executed, and results monitored. Together, these functions provide a. Detect and analyse cyber security events to identify cyber security incidents. Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and.
Things to help you Identify, Prevent, Detect, and Respond to Cyber
Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event. Develop and implement the appropriate. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Together, these functions provide a. Detect and analyse cyber security events to identify cyber security incidents.
Detect And Analyse Cyber Security Events To Identify Cyber Security Incidents.
Develop and implement the appropriate. Together, these functions provide a. Govern, identify, and protect outcomes help prevent and prepare for incidents, while govern, detect, respond, and recover outcomes. Ensure risk responses are identified and prioritized, executed, and results monitored.
The Csf 2.0 Is Organized By Six Functions — Govern, Identify, Protect, Detect, Respond, And Recover.
Learn how the detect function defines the appropriate activities to identify the occurrence of a cybersecurity event.