Preventing Credential Stuffing - Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a.
Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account.
Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Here, cybercriminals steal the usernames and. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a.
What is credential stuffing and are you putting yourself at risk
Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and.
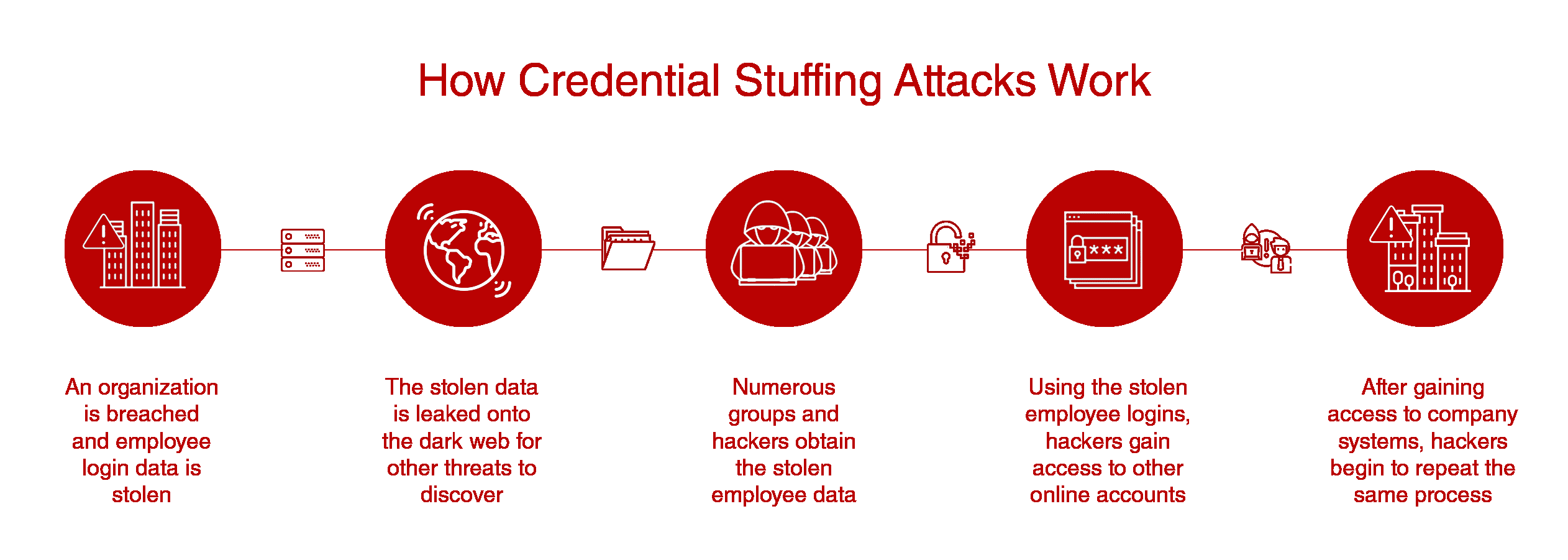
The Anatomy of Credential Stuffing Attacks
Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a.
The WPI Hub Article Identity Theft Credential Stuffing
Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Here, cybercriminals steal the usernames and.
Credential Stuffing Breach Secure Now!
Here, cybercriminals steal the usernames and. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account.
Credential stuffing What it is and how to prevent it NordVPN
Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and.
ONDEMAND WEBINAR Preventing Credential Stuffing Attacks
Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Here, cybercriminals steal the usernames and. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account.
What is credential stuffing and are you putting yourself at risk
Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and.
Credential Stuffing Attacks How to Protect Your Web App from Bots
Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Here, cybercriminals steal the usernames and. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account.
Proactive Tips for Preventing Credential Stuffing Attacks Lazarus
Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Here, cybercriminals steal the usernames and. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a.
Preventing credential stuffing attacks with IPinfo Use Cases IPinfo
Here, cybercriminals steal the usernames and. Learn about credential stuffing, how to detect it, and how to prevent it from impacting your organization. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a. Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account.
Learn About Credential Stuffing, How To Detect It, And How To Prevent It From Impacting Your Organization.
Credential stuffing, also called “password stuffing,” occurs when a criminal steals your login credentials for one account. Here, cybercriminals steal the usernames and. Credential stuffing is a cyberattack method in which attackers use lists of compromised user credentials to breach into a.